Introduction: Why a VPN is No Longer Optional
In 2026, the internet is a battlefield of data collection. Between ISPs (Internet Service Providers) logging your every move, advertisers building detailed profiles of your habits, and the increasing threat of cyber-attacks on public Wi-Fi, browsing “naked” is a massive risk. While hundreds of VPNs claim to offer protection, only a few are built on a foundation of scientific transparency and strict legal sovereignty.
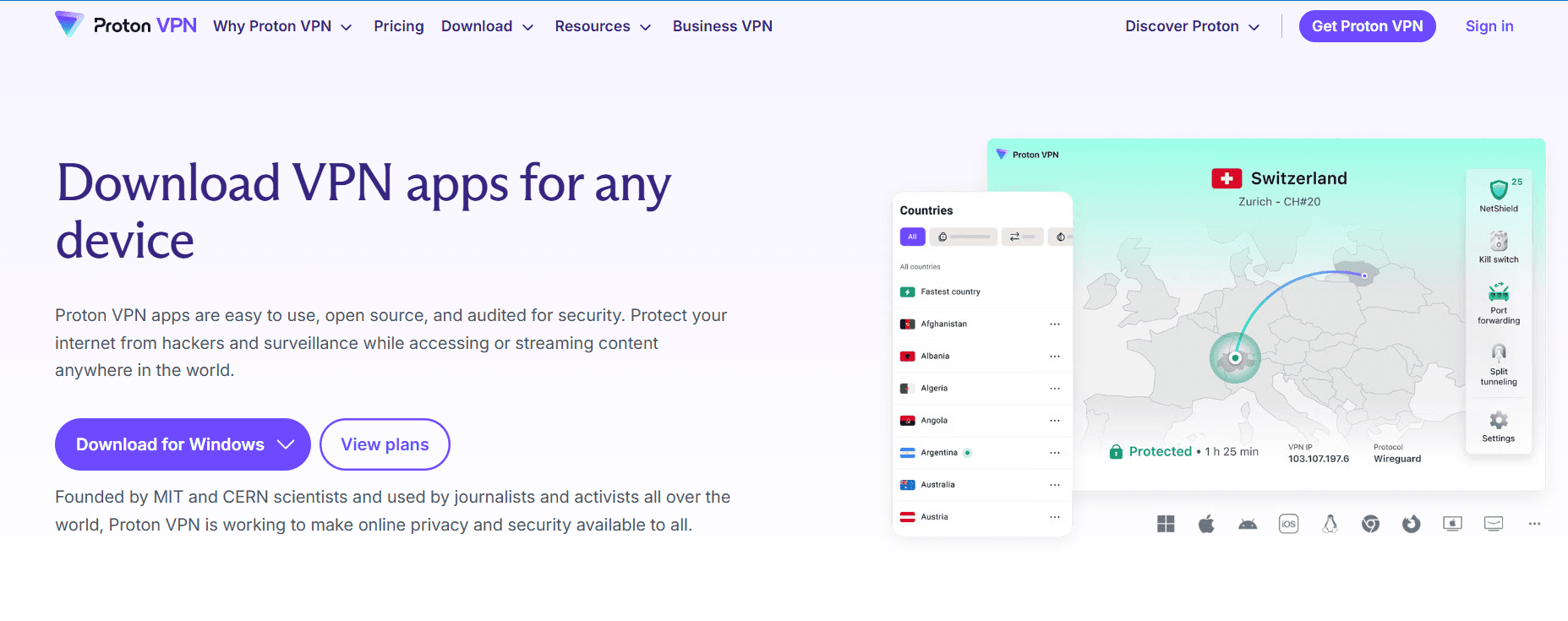
Proton VPN, created by the same team of scientists at CERN who developed Proton Mail, has redefined what users should expect from a virtual private network. It isn’t just a tool to change your IP address; it is a sophisticated security suite designed to provide an impenetrable shield around your digital life. In this 1,500-word definitive guide for Milioudis Tech, we will explore the 2026 features of Proton VPN and why it remains the gold standard for privacy.
1. The Swiss Advantage: Legal Sovereignty
For the readers of milioudis.com, it is vital to understand that location is everything in cybersecurity. Proton VPN is based in Geneva, Switzerland.
Beyond the “Five Eyes”
Most popular VPNs are based in jurisdictions that can be legally compelled to log user data or provide backdoors to intelligence agencies. Switzerland, however, sits outside the US and EU jurisdictions. Swiss law is incredibly strict regarding data privacy. Under current 2026 regulations, Proton VPN cannot be forced to track your browsing history or provide your personal information to third parties.
Audited No-Logs Policy
Proton VPN operates under a strict No-Logs Policy. This isn’t just a marketing slogan; it has been independently audited by top-tier security firms. Even if a government agency seized a Proton server, they would find nothing, because the system is designed to never save your IP address, session lengths, or visited websites in the first place.
2. Technical Architecture: What’s Under the Hood?
The 2026 version of Proton VPN (v4.3.x for Windows/Mac) uses a multi-layered defense system that far exceeds basic encryption.
AES-256 and ChaCha20 Encryption
Proton VPN uses only the highest-strength encryption. All traffic is protected with AES-256, while key exchange is performed with 4096-bit RSA. For mobile users, ChaCha20 is used to provide high security without draining the battery of your smartphone.
Perfect Forward Secrecy
Proton implements Perfect Forward Secrecy. This means that a new encryption key is generated for every single session. Even if a future hacker managed to compromise the key for one of your sessions, all your previous and future sessions would remain safe and encrypted.
Full Disk Encryption
Every single Proton VPN server, even those in remote locations, is protected by Full Disk Encryption. This ensures that if a server is physically stolen or tampered with, the data on it remains completely unreadable to the attacker.
3. Revolutionary Features of the 2026 Edition
Secure Core 2.0: Double-Layer Protection
For users who require maximum anonymity (journalists, activists, or high-level professionals), Proton offers Secure Core.
- How it works: Your traffic is first routed through a high-security server in a privacy-friendly country (Switzerland, Iceland, or Sweden) before it leaves the Proton network to go to your final destination.
- The Benefit: Even if the exit server in a high-risk country is compromised, your real IP address remains hidden behind the hardened Secure Core server.
NetShield Ad-Blocker (Enhanced)
In the 2026 release, NetShield has become a powerhouse. It doesn’t just block ads; it uses a DNS-based filter to prevent your browser from even loading images and scripts from domains known for malware and trackers. This significantly speeds up page loading and reduces data consumption—crucial for mobile browsing.
VPN Accelerator
Traditional VPNs often lose up to 50% of your raw internet speed. Proton’s VPN Accelerator technology uses a custom-built processing engine that can increase connection speeds by over 400% on long-distance hops. This makes Proton VPN the #1 choice for 4K streaming and high-speed gaming in 2026.
4. Bypassing Censorship: Stealth and Smart Protocol
As more countries implement “Deep Packet Inspection” (DPI) to block VPNs, Proton has introduced the Stealth protocol.
How Stealth Works
The Stealth protocol makes your VPN traffic look like regular HTTPS web traffic. This allows users in highly restrictive environments (like schools, offices, or countries with national firewalls) to bypass blocks without detection. Combined with Smart Protocol, the app automatically detects if a specific port or protocol is being blocked and switches to an alternative to keep you connected.
5. Streaming and P2P: Entertainment Without Borders
Proton VPN Plus is optimized for 2026’s high-demand media landscape.
- Global Streaming: In our tests, Proton successfully bypassed geo-blocks for Netflix, Disney+, Hulu, HBO Max, and BBC iPlayer across 120+ countries.
- Tor over VPN: With one click, you can route your traffic through the Tor network, giving you access to Onion sites while maintaining the speed and ease of a VPN.
- Port Forwarding: An essential feature for torrenters and gamers that helps optimize peer-to-peer connections for maximum upload and download speeds.
6. The 2026 Free Version: No Catch, No Limits
One of the reasons Proton VPN is so famous is its Unlimited Free Plan.
- No Data Caps: Unlike competitors who limit you to 5GB or 10GB, Proton offers unlimited data for free.
- No Ads: The free version is supported by paid subscribers, so you are never tracked or shown annoying ads.
- 10 Global Locations: In 2026, the free tier includes servers in the US, Netherlands, Japan, Romania, and Poland, ensuring decent speeds even for non-paying users.
7. Where and How to Download (Official 2026 Sources)
Always avoid “free cracked” versions or third-party mirrors. They are often injected with malware. Use the official Proton infrastructure:
- Official Website: protonvpn.com/download
- Windows & macOS: Download the dedicated installer for the best performance (supports Windows 10/11 and Apple Silicon).
- Linux: Proton offers a full GUI for Linux (Ubuntu, Debian, Fedora), which is a rarity in the VPN world.
- Mobile: Available on the iOS App Store and Google Play Store.
- Privacy Pro Tip: For Android users who want to avoid Google, you can download the APK directly from the Proton website or use F-Droid.
8. Installation and Set-Up Guide
- Sign Up: Create a free or Plus account at
protonvpn.com. - Download: Get the app for your specific OS.
- Log In: Use your Proton Account credentials (the same as Proton Mail/Pass).
- Quick Connect: Click the button to automatically find the fastest server near you.
- Enable Kill Switch: In the settings, turn on the Kill Switch. This ensures that if the VPN connection drops, your internet is cut immediately so your real IP is never leaked.
9. Conclusion: Is Proton VPN Worth It?
Proton VPN is the logical choice for anyone who refuses to compromise on security. While it may be slightly more expensive than some “budget” VPNs, the peace of mind offered by Swiss jurisdiction, open-source apps, and high-speed infrastructure is priceless.
For the followers of Milioudis Tech, Proton VPN is a mandatory tool for any secure digital setup. It is the bridge between a dangerous open web and a private, secure internet.